
It’s a common misconception that larger organizations with hundreds of computers networked and as many or more numbers operating on them would be a prime target for hackers. But the reality is quite the opposite. It is the smaller businesses that are affected by cyberattacks the most, and this has been established through volumes of research and publications.
There can be many reasons for this, such as the fact that larger firms are capable of investing more money toward cybersecurity resources to protect their systems and networks from being hacked. But one key finding in the research is that many small businesses put less priority on cybersecurity. The other reason cited is that the typical hacker looks for personal information, such as bank passwords, which can then be used for financial gain.
Small businesses must, therefore, understand the seriousness of the need to secure their computers.
Before the cybersecurity solutions are enumerated, it may not be out of place here to describe the different kinds of attacks that small businesses may have to face from the hackers. Stealing important data and demanding a ransom to release the data is one of the most frequently observed forms of cyberattacks.
Malware attacks are the most common form of cyberattacks and when this term in used, it practically covers all types of malicious contents, viruses, spyware, ransomware, trojans and so on.
Phishing is another notorious method of breaking into computer systems to inflict damage. As much as the types of attacks abound, the solutions to control these are quite varied too.
Here are some strategies small businesses can take to safeguard against cyberattacks:
1. Have a Policy on Cybersecurity
This is similar to the campaign on achieving quality consistency in the manufacturing sector. Unless the organization as a whole is not on the same page in achieving quality, it can never be achieved.
In the same way, even the smallest of businesses must adopt a clear policy on what IT best practices will be mandatory for every employee. The owner of the business, down to the last one who uses any connected device in the company, should follow the best protocols relating to cybersecurity. Unless the intent is spelt out, understood by all and strictly adhered to, it is never going to happen.
Some of the areas this can be implemented include structured training sessions for all stakeholders. Institute a mechanism to ensure that all staff members of all levels follow the set procedure. This may include a separate user ID and password for each person using the system.
Training them to create solid passwords so that an intending hacker cannot easily guess the code is also important. The very last person in the office must be clued in on how to handle the computers, avoid clicking on ads or opening suspicious emails, or clicking on unwanted attachments or links in the emails. If you are generating and storing data, that may not be accessible to all members of the staff. It must be need-based and has to be allowed only with specific permissions.

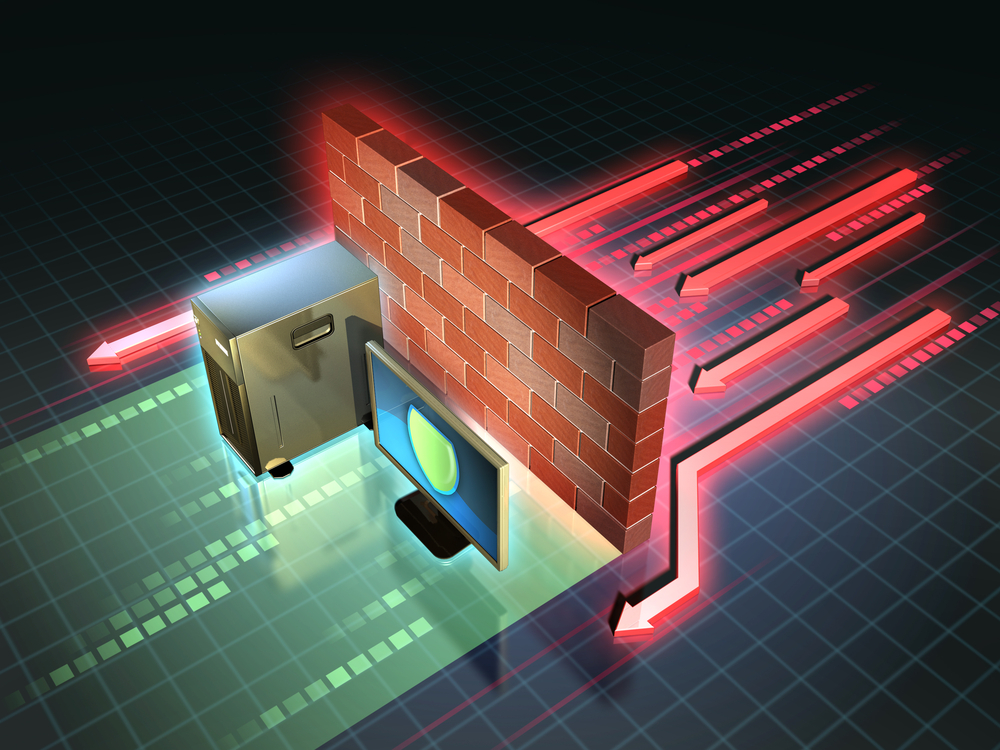
2. Ensure the Firewall Is Up
Computer systems have a built-in firewall to safeguard against possible malware attacks. Ensure it is turned on. The system may keep warning you if the firewall is turned off for some reason. On such occasions, just turn it on promptly.
There are also external firewalls available to ensure an additional barrier between your computer or server and the internet service provider’s incoming supply point. If you are the owner of the business and you use a computer from home for business purposes too, ensure the firewalls are up at the residence as well.
3. Keep Employees Updated
It is typical of small businesses to employ people on temporary or hourly rates. This means, every now and then a new person would be using the systems within the company for various tasks. It is essential that all employees, whether employed for a day or in permanent rolls, must be aware of the risks associated with cybersecurity threats and they must be careful while using the systems.
Opening their personal emails with malicious attachments can destroy in less than a minute what you have built over the years, in terms of business data and other critical information related to the business.
Include all new recruits into an introduction module where they must pass through a session in which the full cybersecurity protocol is explained and demonstrated. Only when the person shows the confidence of having understood all the aspects should they be allowed to use the computer systems and networks on an independent basis.

4. Backup Your Data Periodically
Enforcing the cybersecurity policy strictly and overseeing its implementation can definitely yield results. You can, however make it safer by backing up your data in the cloud or an external storage for retrieval when needed. Even if you leave some of the documents in your server and it is breached, you will feel safe that you have the backup elsewhere to access the information.
This task may be assigned to someone in the organization and the responsibility fixed so that there is no failure on this. Another option that makes sense would be the outsourcing of this task to an external company. For example, if your small business is located in the northeastern part of Illinois, contacting an IT support provider in Chicago that offers data backup solutions would be a great choice. All data from any resource within the company must be stored in a central place that must be extra-protected.

5. Install the Best Anti-Malware Software
This is an advice you cannot overlook. When even individuals using a PC or laptop have to have the most effective anti-malware program installed, it requires no emphasis on how critical it is for businesses.
There are many products available in the market. You can do a due diligence exercise checking on user reviews posted online. Even if you have to pay for the best ant-malware program, get it and install it.
But it does not stop with this; you should also be alert to the updates being issued by the developers of the program. This is vital because hackers are constantly inventing new ways to mount cyberattacks, and your anti-malware program will need to be equally capable of stopping new attacks. The best way to ensure this is to keep your software up-to-date.

6. Introduce Tougher Authentication
Experts believe that one of the requirements for small businesses to beef up the security of their computer systems is to insist on more than a simple password to access the systems allotted to them.
The best suggestion is to include the employee’s mobile number as an additional layer. This suggestion is based on the premise that a hacker may not be able to get hold of both the passcodes. It will definitely make the systems more secure.
Multi-factor authentication provides an additional layer of security by requiring more than one form of verification. Methods such as time-based one-time passwords or physical security keys enhance protection against unauthorized access. Utilizing MFA ensures that even if a password is compromised, the additional step makes it harder for intruders to gain access to systems.
Beyond enhancing security, adopting MFA demonstrates a commitment to protecting sensitive information. This extra measure fosters trust with clients and partners, who count on businesses to safeguard personal and financial data. Encouraging employees to use MFA even for personal accounts further cultivates a culture of security awareness within the organization.
The same holds for quickly withdrawing the permission when an employee is leaving the organization. Whatever the circumstance, pleasant or not so pleasant, those few moments could be the most critical. Many organizations realize much later that former employees managed to steal important data after their last day on the job. Keeping a close eye on this is very critical to any small business.

7. Include Other Devices in the Security Net
Increasingly, consumers are using connected devices like smartphones and smartwatches for business purposes. While drawing up the total security plan, remember to include these devices too in the loop and the same yardsticks should be applied for authentication and access.
With the increasing use of personal devices for work, managing these devices is key to maintaining security. Implementing policies that dictate secure use and management of employee-owned devices helps protect sensitive data. Ensuring that security software is consistently updated on all devices reduces the risk of unauthorized access. Training employees about potential threats related to their devices is equally important.

8. Hold Mock Audit Sessions
One of the solutions suggested by experts is to hold surprise checks on the integrity of your system.
There are two ways to do this. First, you could get your systems engineer on staff to plant a virus and allow the employees to trace it and remove it. This is similar to the fire drills done in many institutions to prepare the staff to face an eventuality.
The other option is to hire an expert from outside to do almost the same, but the added advantage would be the professional would do a more thorough job and use the opportunity to check and give you a comprehensive report on the security-preparedness of your system.
Regular cybersecurity audits play a significant role in maintaining the security of small businesses. These audits help identify vulnerabilities in systems and practices by assessing current security measures. Conducting thorough audits ensures that security protocols remain effective against new threats. Frequent audits also strengthen compliance with cybersecurity standards, giving businesses peace of mind.
Regular audits not only confirm adherence to existing security measures but also help in adapting to ever-changing cybersecurity landscapes. The shifting nature of cyber threats requires that businesses stay ahead by identifying potential gaps in their defenses systematically. Incorporating both internal and external audits leverages varied expertise, ensuring thorough inspection and compliance with industry standards.

9. Some Suggested Security Packages
While the normal antivirus software package does the job, there are specialized offerings and resources for small and medium sized businesses which have proved to be very useful over time. These include Comodo, Riverbed Xirrus Wi-Fi Inspector, Stay Safe Online, the Federal Communication Commission’s Small Biz Cyber Planner, among other resources.
You can do a detailed study on the features of each of these software solutions and how they can be useful to your business in protecting from all forms of security threats. If you want to try out the free antivirus packages before making a final decision, then you can do the trial of each one and then stick to the best of the lot.
Role of Cyber Insurance
Cyber insurance is an important consideration for small businesses to mitigate financial risks associated with cyberattacks. This type of insurance can cover the costs incurred from data breaches, business interruptions, and even extortion demands. Understanding the coverage options available helps businesses choose a policy that aligns with their security needs and potential risks.
Incident Response Plan
Having an incident response plan in place is essential for dealing with cyberattacks effectively. This plan should clearly outline the steps to take during and after an incident, assigning roles to key team members. Regular drills and updates to the plan help ensure everyone is prepared to manage an attack quickly, minimizing impact.
The incident response plan should also encompass post-incident analysis. Evaluating how the attack was handled offers valuable insights into what worked well and what areas require improvement. Sharing findings within the organization increases collective knowledge, fortifying the team’s defense strategies for the future.
Cybersecurity is an aspect that has emerged center-stage for businesses as every passing year sees increasing cases of hacking and data breaches. Surprisingly, smaller businesses are seen by these attackers as easier targets. There’s no point in regretting after one has been a victim of a cyberattack. You have to take steps before you are subject to a hack.
Being smart in your business means learning from others’ mistakes and forming your own best-practices to effectively lead your organization. In the final analysis, even if you have to spend a small sum of money to add stronger protection to your computer system, you may want to commit to those expenses in order to avoid the risks of a crippling cyberattack.
More people have taken losses due to inadequate security steps on their systems than there are those who have taken the precautions to save their systems from a hack.
As mentioned above, the knowledge that cybersecurity is important, the intent to keep your systems safe and the commitment to be firm with the practices are all the ingredients for a satisfying business operation keeping the hackers at bay.
Author Bio
Sophie is a marketing specialist at Security Gladiators. A writer by day and a reader by night, she is specialized in tech and cybersecurity. When she is not behind the screen, Sophie can be found playing with her dog.
Last Updated on March 13, 2025 by Ian Naylor
One thought on “9 Cybersecurity Solutions for Small Business”